Why Crypto Hack Matters More Than Ever in February 2026
Why Crypto Hack Matters More Than Ever in February 2026
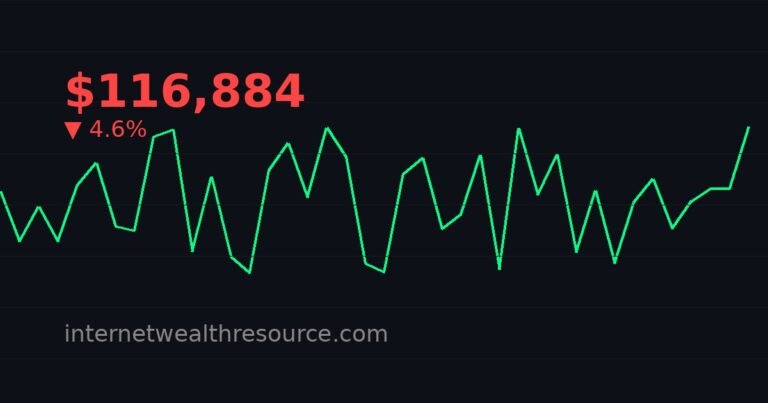
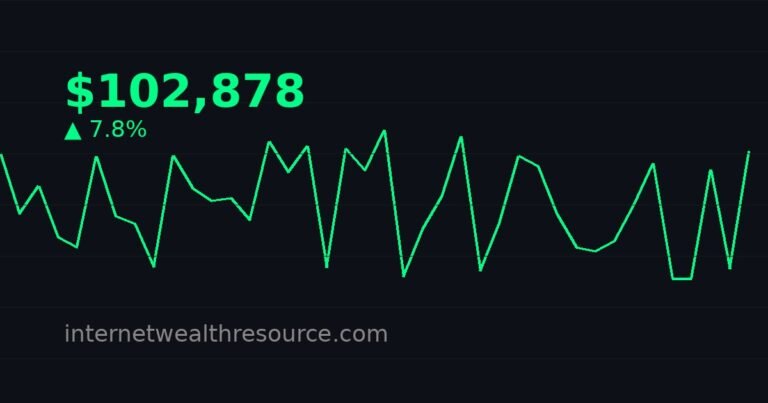
The digital gold rush of the mid-2020s has hit a familiar, chilling snag. As Bitcoin trades at $63,174, down nearly 5% in 24 hours with a staggering $48.6 billion in volume, the market is jittery. Yet, the volatility isn’t solely about macroeconomic whispers or ETF flows. In February 2026, the specter of the sophisticated crypto hack has re-emerged as the single most critical non-financial risk to investor portfolios and ecosystem stability. The stakes are higher than ever, with institutional capital locked in DeFi protocols and real-world assets tokenized on-chain. Understanding this threat is no longer optional for preservation of capital.
The 2026 Landscape: A High-Value Target
The current market data tells a story of immense, concentrated value. Bitcoin’s $1.26 trillion market cap represents a mature asset class, but the surrounding decentralized finance (DeFi) and Layer-2 ecosystems hold hundreds of billions more. Unlike the “wild west” days, today’s attacks are not just about hot wallet thefts. They are complex, surgical strikes on protocol logic, cross-chain bridges, and the oracles that feed data to multi-billion dollar markets. A single successful crypto hack in this environment can trigger cascading liquidations and a crisis of confidence that sends the entire market, as we see today, into a sharp corrective spiral.
Anatomy of a Modern Crypto Hack: Beyond the Headlines
To defend against a threat, one must understand its evolution. The classic exchange breach is now almost passé. The frontier of digital theft has moved to the core infrastructure of Web3.
The Bridge Problem
Cross-chain bridges, essential for interoperability, remain the “honeypots” of crypto. They require locking up immense liquidity in smart contracts, creating a target too tempting for hackers to ignore. A breach here can see losses in the hundreds of millions instantaneously, draining liquidity from multiple chains and freezing asset movement.
Oracle Manipulation
DeFi protocols rely on oracles for external price data. By manipulating this data feed—often through flash loan attacks—hackers can create false liquidation conditions or borrow far more than collateral allows. This type of crypto hack exploits the very trust mechanism that DeFi is built upon.
Supply Chain Attacks on Open-Source Code
With developers routinely using open-source libraries and forked code, a vulnerability inserted into a common tool can compromise thousands of protocols simultaneously. This represents a systemic risk of unprecedented scale.
Market Impact: More Than Just Stolen Funds
The immediate financial loss from a hack is devastating for its victims, but the secondary market impact is what every investor should fear. The 4.83% dip in Bitcoin today, amid high volume, exemplifies how negative security news catalyzes sell-offs. The mechanisms are clear:
- Contagion Fear: News of a major exploit triggers panic about interconnected protocols. Investors rush to withdraw funds, often crashing token prices and causing “bank runs” on DeFi platforms.
- Liquidity Crunch: Stolen funds are often quickly swapped for stablecoins or ETH, creating sell pressure. Furthermore, locked liquidity in a compromised protocol vanishes, tightening market conditions.
- Regulatory Scrutiny: Each major hack provides ammunition for regulators advocating for stricter controls, which the market often interprets as bearish for the permissionless innovation narrative.
In essence, a crypto hack acts as a severe stress test, revealing leverage points and fragile interconnections in the system.
Actionable Insights for the 2026 Investor
In this environment, security is not a technical afterthought—it is the cornerstone of investment strategy. Here is how to adapt:
- Due Diligence is Paramount: Before investing in any protocol, research its audit history. Look for multiple audits from reputable firms, and check if the team has a bug bounty program. A non-audited protocol in 2026 is an unacceptable risk.
- Embrace Cold Storage: For significant holdings, especially Bitcoin, a hardware wallet remains the gold standard. The mantra “not your keys, not your crypto” is complemented by “not in cold storage, not truly safe.”
- Diversify Across Security Models: Don’t concentrate all assets in one smart contract ecosystem or chain. Spread exposure across different types of custody solutions (self-custody, insured custodians) and Layer-1 blockchains to mitigate single-point-of-failure risk.
- Monitor Social Intelligence: Follow security researchers and firms on social media. Often, vulnerabilities are discussed or hinted at in specialized circles before they explode into mainstream news, giving alert investors a crucial window to act.
Bullish vs. Bearish: Security as the Dividing Line
The market’s trajectory in 2026 will be split by its response to the hacking threat.
The Bull Case: Proponents argue that each major crypto hack forces the industry to innovate stronger security. We’re seeing the rise of institutional-grade custody, insurance protocols like Nexus Mutual, and formal verification of smart contracts. This painful evolution, they say, is building an antifragile system that will eventually make traditional finance look porous by comparison. The current dip is a buying opportunity in a long-term hardening process.
The Bear Case: Skeptics contend that the complexity of DeFi and cross-chain systems is outstripping the industry’s ability to secure them. They see the recurring bridge exploits and oracle failures as a fundamental flaw, not a growing pain. If billion-dollar hacks continue, institutional adoption will stall, and regulators will impose draconian rules that stifle growth. The February 2026 sell-off could be a preview of a prolonged bear market triggered by a catastrophic, systemic security failure.
Conclusion: The Unseen Battle Defining Crypto’s Future
As of February 24, 2026, the battle lines are drawn not on price charts alone, but in the lines of code securing $1.26 trillion in Bitcoin value and the sprawling DeFi ecosystem around it. The market’s negative reaction to any security incident is a sign of both its maturity and its persistent vulnerability. For the savvy investor, navigating this space requires a dual mindset: opportunistic optimism about blockchain’s potential combined with a relentless, paranoid focus on security hygiene. The next chapter of cryptocurrency adoption will be written not just by developers and traders, but by the white-hat hackers and auditors working to ensure that the trustless system is, above all, trustworthy. Your portfolio’s survival depends on recognizing that a single crypto hack is no longer an isolated event—it is a market-moving force.
\n\n
More Crypto News
\n\n
Explore More
\n\n
Source: CoinGecko